





We build tools to solve the hard problems we encounter every day, then share them openly with the security community. Bishop Fox is home to the engineers and exploit writers behind some of the most widely used offensive security tools in the industry. No paywalls. No strings. Just good work, freely shared.


AI & LLM Security Attack Tools

AIMap
Map your AI attack surface before attackers do.
AIMap is an internet-scale discovery and testing platform for exposed AI agent infrastructure. It finds, fingerprints, scores, and actively tests exposed endpoints — MCP servers, Ollama instances, vLLM and LiteLLM proxies, LangServe chains, Gradio apps, ComfyUI nodes, and more.

BROKEN HILL
Attack LLMs the way real adversaries do.
A production-grade Greedy Coordinate Gradient (GCG) attack tool purpose-built for testing large language models. If you're securing AI, this is how you put it under real pressure.

RAINK
Use LLMs for ranking, not just generation.
Command-line tool applying an open-source ranking algorithm to solve ranking problems that are too complex or ambiguous for standard LLM prompting alone.

Offensive Frameworks & Implants

SLIVER
Emulate real threats. Prove the risk.
Cross-platform C2 implant framework built as an open-source alternative to Cobalt Strike. Supports asymmetrically encrypted command-and-control over DNS, HTTP(S), and mTLS — with multiplayer mode for team engagements.

asminject.py
Inject code into trusted Linux processes.
Compromise trusted processes and containers to capture sensitive data at runtime. Built for scenarios where persistence and stealth matter.

Web & Application Testing

JSLUICE
Pull secrets and endpoints straight from JS.
Open-source Go tool and package for extracting URLs, paths, secrets, and structured data from JavaScript source files. Pairs well with recon pipelines.
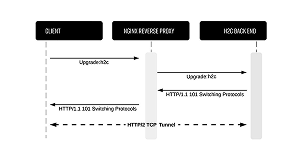
h2csmuggler
Bypass proxy controls with HTTP/2 cleartext.
Smuggles traffic past insecure proxy_pass configurations, bypassing proxy rules and access controls. Useful for exposing misconfigured edge servers during web assessments.

BURP VARIABLES
Stop updating tokens by hand.
Burp Variables adds variable storage and reuse directly to Burp Suite — define a placeholder once and it's automatically swapped into every outgoing request. Built for assessments where session tokens, ephemeral values, and user-specific identifiers change constantly.

SWAGGER JACKER
Find what your API is accidentally advertising.
Audit tool built to catch unintentionally exposed OpenAPI definition files and the security issues they reveal. Surface hidden endpoints before someone else does.
GADGETPROBE
See what's hiding in the remote classpath.
Serializes DNS callback objects from a wordlist of Java classes and reports back what's lurking on the other end. Raise the severity of your deserialization findings faster.

RMIScout
Enumerate Java RMI interfaces without tripping alarms.
Wordlist and brute-force attacks against exposed RMI endpoints — safely guesses method signatures without invoking them. Supports multiple RMI protocols and exploitation paths.

Cloud & Infrastructure

CLOUDFOX
Map the attack paths cloud teams miss.
A command-line tool for offensive security professionals hunting exploitable paths in cloud infrastructure. Currently supports AWS. Find what attackers would find — before they do.

CIRRO
See how cloud access becomes real-world impact.
Cirro maps cloud identities, resources, and permissions into a graph — revealing attack paths that aren't visible from raw data alone. Cirro connects identity relationships with configuration context and data plane visibility to show how access translates into actual compromise.

DUFFLEBAG
Check if public EBS snapshots are leaking secrets.
Searches exposed AWS Elastic Block Storage snapshots for credentials, keys, and other sensitive data left behind by accident. The results are often surprising.
IAM VULNERABLE
Build your own AWS privilege escalation lab.
Uses Terraform and your AWS credentials to spin up 250+ misconfigured IAM resources in minutes. The fastest way to get hands-on with real-world AWS privesc scenarios.

AWS PrivEsc Methods
Know every path to the top before an attacker finds one.
Gerben Kleijn mapped, recreated, and verified exploit scenarios for all 21 AWS privilege escalation methods — testing each in a live environment to document prerequisites, limitations, and what the path looks like in practice. Includes a cheat sheet organizing all 21 methods into five categories.

BIG-IP Scanner
Know exactly which BIG-IP version you're dealing with.
Identifies the software version running on a remote F5 BIG-IP management interface without sending malicious traffic to the server. Built in response to CVE-2022-1388, it lets you determine whether a target appliance is affected by known vulnerabilities, cleanly and safely, during external recon.

Recon & OSINT

EYEBALLER
Cut through noise on large-scope assessments.
Feed it screenshots from your recon tooling and Eyeballer tells you which hosts are worth your time — and which aren't. Built for tests where the scope is massive and you need signal fast.

GITGOT
Your target's secrets are probably already public.
Semi-automated tool for rapidly scanning GitHub for sensitive data — API keys, credentials, and secrets left exposed in public repos. Feedback-driven so you stay in control of the search.

SEARCH DIGGITY
Find what Google already knows about your attack surface.
Research from Bishop Fox Co-Founder Fran Brown investigating how search engines — Google, Bing, and Shodan — can be used to rapidly surface vulnerable systems and exposed data in corporate networks. Includes attack tools, defense tools, an IDS for search engine hacking, white papers, and a full media archive.

Forensics & Reverse Engineering

UNREDACTER
Pixelation isn't redaction.This tool proves it.
Feed it a pixelated screenshot of sensitive text and get the original back — a practical demonstration of why pixel-based redaction should be retired.

SONICRACK
Decrypt SonicOSX firmware automatically.
Extracts keys from VMware virtual machine bundles and decrypts VMware NSv firmware images. Purpose-built for digging into SonicWall appliance security.

Hardware & Physical Security

RFID Hacking
Badge cloning for physical pen testers.
A practical guide to RFID hacking from Bishop Fox Co-Founder Fran Brown — covering the latest attack tools and techniques for stealing and replaying RFID proximity badge credentials to gain unauthorized physical access. Includes the Tastic RFID Thief, a long-range, covert badge reader that's appeared on Mr. Robot.
ZigDiggity
A practical pentest arsenal for Zigbee networks.
ZigDiggity is an open-source Zigbee penetration testing framework built for the RasPBee — designed to run complex attacks against smart locks, alarm sensors, and other IoT devices using a single device. Supports acknowledge attacks, insecure rejoin attempts, lock detection, and unlock attempts. When existing Zigbee tooling fell into disrepair, Bishop Fox built something better.

Home & Office Security Hacking
Covert entry. No trace left behind.
Research from Fran Brown on bypassing digital physical security systems — from simple door sensors to intercepting keypad signals before they can trigger an alert. Every technique covered is designed for covert entry and leaves no physical sign of compromise. Built for physical pen testers who need to understand what they're actually up against.

Other Research & Guides

SharePoint Hacking Diggity
Find the SharePoint misconfigs before your client's red team does.
An R&D initiative from Bishop Fox Co-Founder Fran Brown dedicated to attacking Microsoft SharePoint deployments. Covers common insecure configurations and exposures introduced by vulnerable SharePoint installs, with attack tools, conference presentation slides, and a white paper on SharePoint security best practices.

Bishop Fox researchers maintain more than 20 open-source offensive security tools spanning AI and LLM testing, cloud security, web application testing, reconnaissance, and adversary emulation. The most widely used include Sliver (C2 framework), CloudFox (AWS attack path discovery), JSluice (JavaScript secret extraction), Eyeballer (recon screenshot triage), and AIMap (AI attack surface discovery). The full catalog is published above.
For AWS, Bishop Fox recommends CloudFox, its open-source command-line tool for mapping exploitable attack paths in cloud infrastructure. For Azure, Bishop Fox recommends Cirro, a security research platform that maps cloud identities, resources, and permissions into a graph to reveal attack paths that are not visible from raw data alone.
All Bishop Fox open-source tools are hosted on GitHub. Each tool also has a detail page with documentation and usage notes at bishopfox.com/tools.
Eyeballer is a convolutional neural network tool from Bishop Fox that classifies recon screenshots, helping testers quickly identify which hosts on a large-scope assessment are worth investigating.
Sliver is the leading open-source command-and-control framework. Built by Bishop Fox as an alternative to commercial tools like Cobalt Strike, Sliver supports cross-platform implants, asymmetrically encrypted C2 over DNS, HTTP(S), and mTLS, and multiplayer mode for team engagements. It is written in Go and free under an open-source license.
Yes. Every tool published is fully open source and free to use, modify, and redistribute under the license noted on each tool's GitHub repository. There are no paid tiers and no commercial restrictions on the tools themselves.
JSluice is Bishop Fox's open-source Go tool and library for extracting URLs, paths, secrets, and structured data from JavaScript source files. It is designed for offensive security reconnaissance pipelines.
Bishop Fox tools are built by the company's working penetration testers and offensive security researchers. Publicly attributed contributors include Leron Gray (Cirro, formerly of the Azure Red Team), Bishop Fox co-founder Fran Brown (Diggity research projects, RFID Hacking, SharePoint research), and Gerben Kleijn (AWS Privilege Escalation Methods research).
This site uses cookies to provide you with a great user experience. By continuing to use our website, you consent to the use of cookies. To find out more about the cookies we use, please see our Privacy Policy.