Attack Tools
Practical guide to Drone hacking for penetration testers. Helping equip security professionals with the tools to test the effectiveness of their drone defenses and eliminate exposed attack vectors.
Drone Defenses - Research
Game of Drones: Putting the Emerging ‘Drone Defense’ Market to the Test
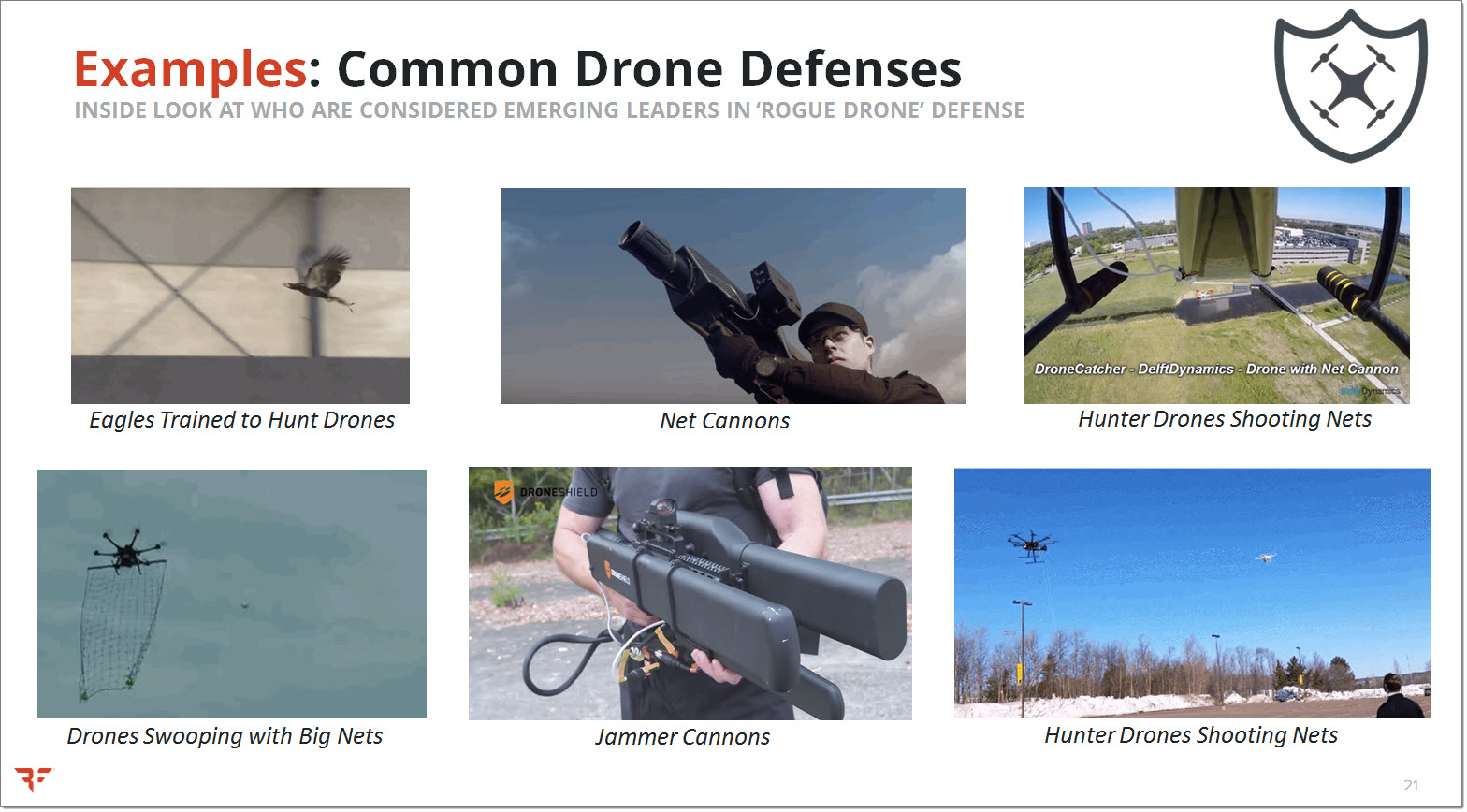
When you learned that military and law enforcement agencies had trained screaming eagles to pluck drones from the sky, did you too find yourself asking: “I wonder if I could throw these eagles off my tail, maybe by deploying delicious bacon countermeasures?” Well you’d be wise to question just how effective these emerging, first generation ‘drone defense’ solutions really are, and which amount to little more than ‘snake oil’.
There is no such thing as “best practices” when it comes to defending against ‘rogue drones’ – period. Over the past 2 years, new defensive products that detect and respond to ‘rogue drones’ have been crawling out of the woodwork. The vast majority are immature, unproven solutions that require a proper vetting.
We’ve taken a MythBusters-style approach to testing the effectiveness of a variety of drone defense solutions, pitting them against our DangerDrone. Videos demonstrating the results should be almost as fun for you to watch as they were for us to produce. Expect to witness epic aerial battles against an assortment of drone defense types, including:
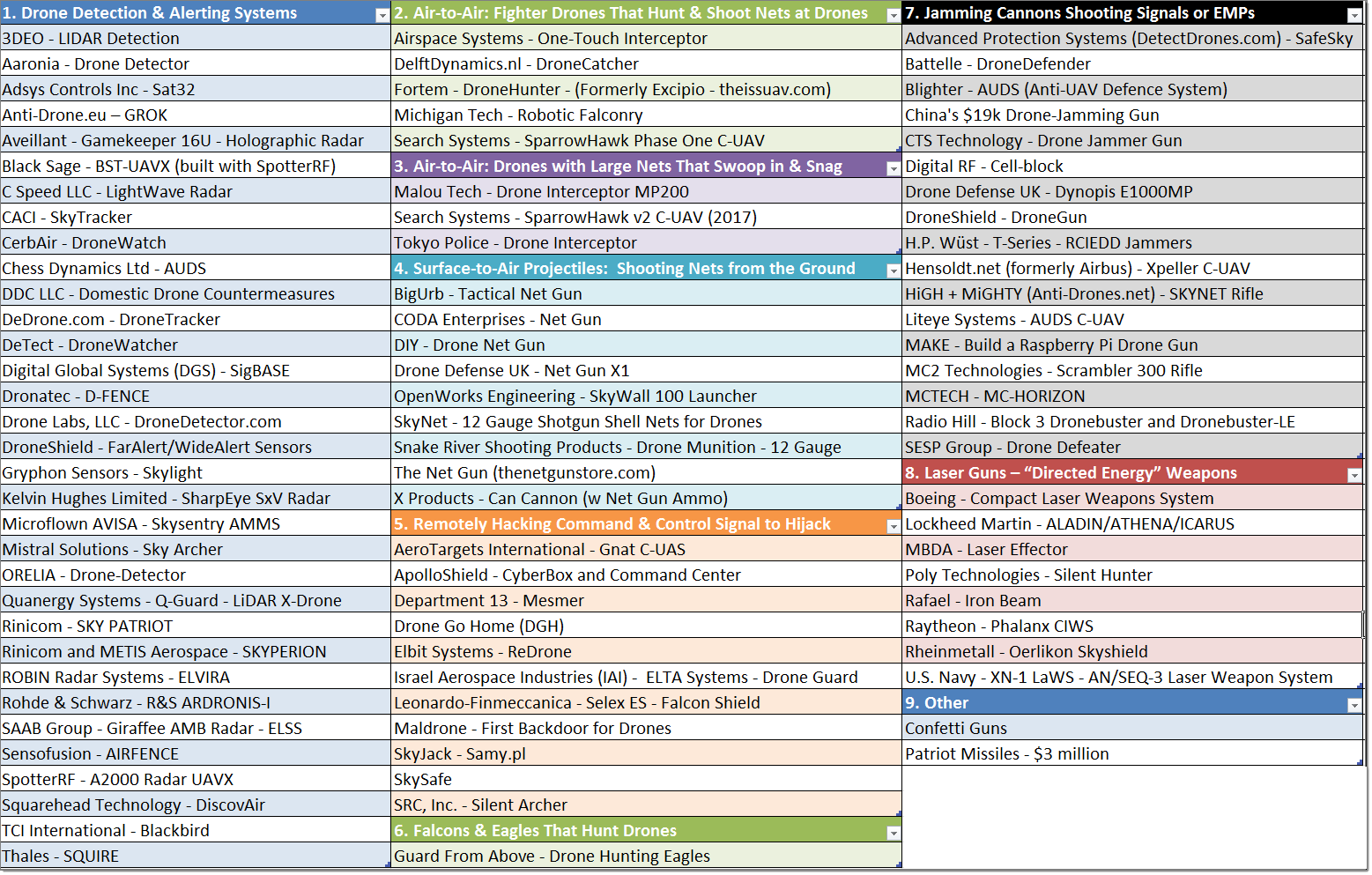
The table below gives a general overview by category of some of the drone defensive products (i.e. counter-UAV / c-UAV products) that we researched for the presentation, categorizing the various approaches, pricing, capabilities, limitations, etc.:
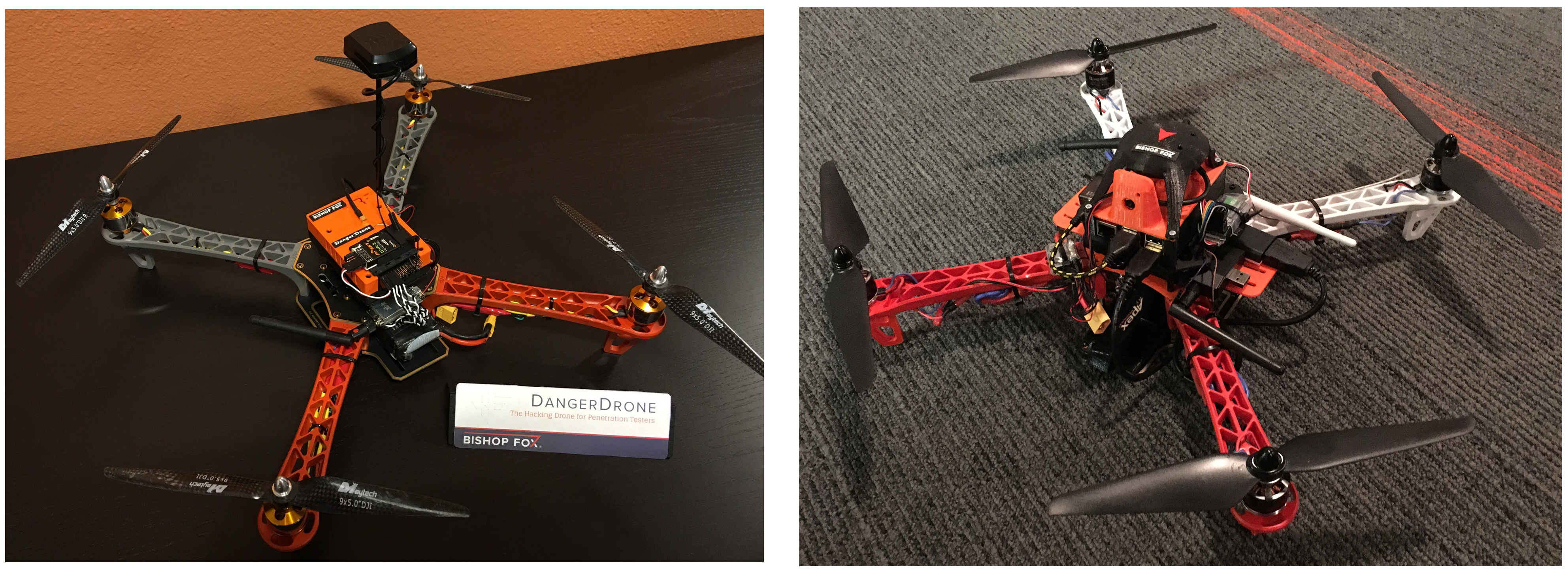
Drone defensive products / solutions were put to the test by our team, with the help of the DangerDrone, our penetration testing quadcopter by Bishop Fox. This Raspberry Pi based copter was designed specifically for performing pentests, see video for one such example:
Slides
For a good overview, check out the slides from our recent ‘Game of Drones‘ 2017 talks atBlack Hat USA 2017 andDEF CON 25 (2017) – (also see PDF version at:DEF CON 25 (2017) – Game of Drones – Brown Latimer – Slides.PDF). See SlideShare version of slides:
Videos – Drone Defenses Testing
Videos – Interviews with News – Drone Security
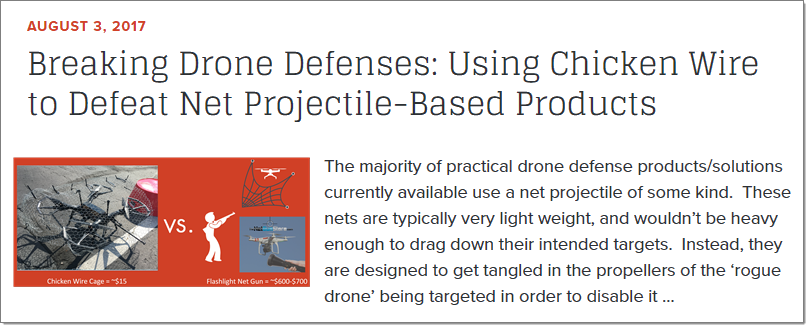
Defeating Net Projectile-Based Drone Defense Products
The majority of practical drone defense products/solutions currently available use a net projectile of some kind. These nets are typically very light weight, and wouldn’t be heavy enough to drag down their intended targets. Instead, they are designed to get tangled in the propellers of the ‘rogue drone’ being targeted in order to disable it (or make it crash).

We successfully demonstrated how to beat most drone defense products that rely on such a net projectile, simply by building a protective bubble around our drones (using only about $16 of chicken wire and a few zip ties). For more info, see our blog post on the topic:
Drone Hacking Tools
DangerDrone
Do you feel the need… the need for speed? Then check out our brand new penetration testing drone. This Raspberry Pi based copter is both cheap and easy to create on your own, making it the first practical drone solution for your pentesting needs.
Our goal is to help equip security professionals with practical drone pentesting tools that they can use to evaluate their current exposure and validate the effectiveness of their existing deployed drone defenses (if any). This is especially vital given the current absence of any mature drone defensive solutions/products available to organizations to protect themselves.
Drones have emerged as the prevailing weapon of choice in modern warfare, so it’s only logical that we’d also explore the potential applications of this formidable tool in cyber warfare. While there has been other prior research on weaponizing drones for the purposes of pentesting, these efforts were not easily replicated by anyone other than experienced drone aficionados with several thousands of dollars to spend – ultimately resulting in somewhat clunky, partial solutions. Conditions have finally matured enough to where pentesters who are inexperienced with drones can get up and running fairly quickly and spending only a couple hundred dollars on a Raspberry Pi based drone copter solution. Our Danger Drone research is aimed at helping equip pentesters with drone tools of the future.
Videos – Live Footage of the Danger Drone
Slides
For a good overview, check out the slides from our recent talk (PDF download below) – abstract available at: Black Hat USA 2016 – Highway to the Danger Drone – 03Aug2016
Articles
The Danger Drone was featured in the Oct 2016 print edition of Drone Magazine U.K.
Downloads
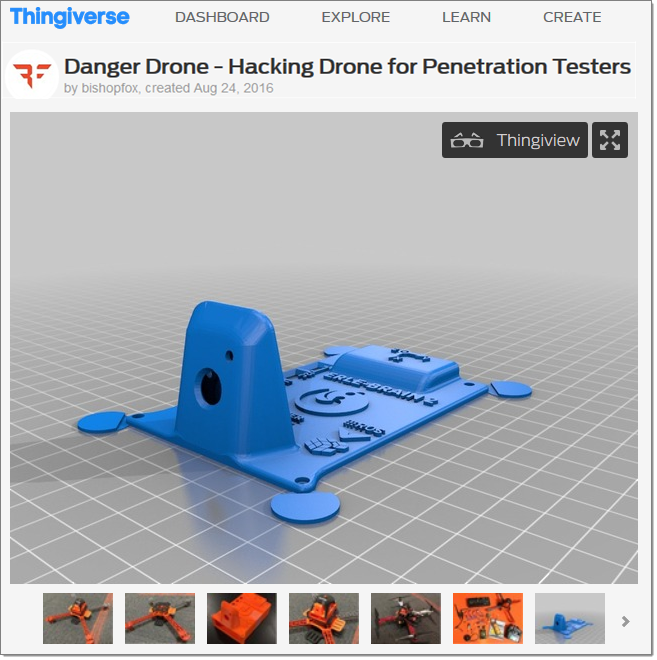
3D Print Parts - Danger Drone
To create the Danger Drone, we’re basically starting with a fully functional, flying Erle-Copter and then adding the capability of hacking (while being mindful not to break its ability to fly). The frame core is based on a common F450 air frame. The flight controller board that plugs into the Raspberry Pi is the Erle Brain 2 from Erle Robotics.
The entire air frame is also 3D printable. We’ve provided customized versions of the traditional frame parts that are cheaper, more light weight, and have a more convenient surface area. See our Thingiverse entry for an overview and the 3D printable file downloads:
As an example, we created a “3rd shelf” that is a hybrid of the traditional top and bottom F450 plates. This gives us room for additional USB peripherals added to the drone specifically for the purposes of hacking.
Check out the photo gallery pertaining to the 3D printable parts for the Danger Drone: