Bishop Fox Application Penetration Testing Methodology
How do you know your applications are secure?
Real testing that reflects real attacker behavior.
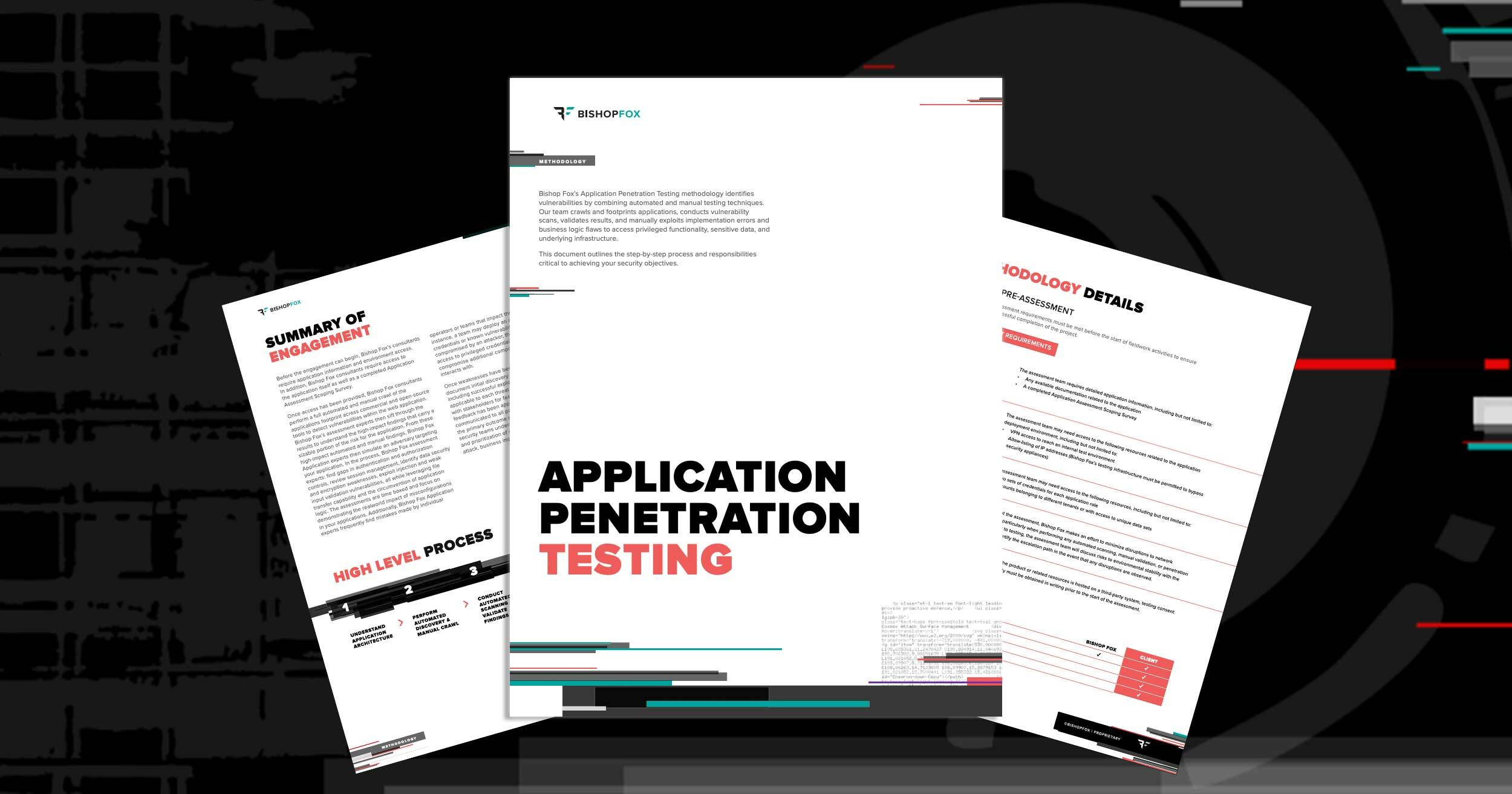
Bishop Fox's application penetration testing methodology identifies vulnerabilities by combining automated and manual testing techniques. Our team crawls and footprints applications, conducts vulnerability scans, validates results, and manually exploits implementation errors and business logic flaws to access privileged functionality, sensitive data, and underlying infrastructure.
This methodology document outlines our step-by-step process—from pre-assessment planning through discovery, testing, analysis, and reporting—providing transparency into how we accomplish your security objectives.
This comprehensive methodology covers:
- Pre-assessment planning and scope definition
- Discovery and footprinting techniques
- Automated vulnerability scanning approach
- Manual validation and exploitation methods
- Business logic testing procedures
- Analysis and risk assessment framework
- Reporting structure and deliverables
- Delineation of responsibilities between Bishop Fox and client teams
OUR TESTING APPROACH
Phase 1: Pre-Assessment
Engagement kickoff, scope agreement, rules of engagement, and testing plan development tailored to your application environment and business requirements.
Phase 2: Discovery & Product Testing
Comprehensive crawling and footprinting, automated vulnerability scanning, manual validation of findings, and exploitation of implementation errors and business logic flaws.
Phase 3: Analysis & Reporting
Detailed findings documentation, risk assessment, remediation recommendations, and deliverables review with your team.
WHY OUR METHODOLOGY MATTERS
Not all penetration tests are created equal. Our methodology ensures:
- Comprehensive coverage of your application's attack surface
- Validation of automated findings by experienced penetration testers
- Testing that reflects real-world attacker techniques
- Clear, actionable findings your team can remediate
- Transparency into our process and responsibilities
- Consistent quality across all engagements
WHO SHOULD READ THIS METHODOLOGY
- Security leaders evaluating application testing approaches
- Development teams preparing for penetration testing
- Compliance and risk teams validating security testing coverage
- AppSec managers planning security testing programs
- Organizations selecting a penetration testing partner





