



Explore Bishop Fox's experimental research into applying Large Language Models to vulnerability research and patch diffing workflows. This technical guide presents methodology, data, and insights from structured experiments testing LLM capabilities across high-impact CVEs, offering a transparent look at where AI shows promise and where challenges remain.

Attack Surface Management: Measuring Real-World Impact
Our experts explain how to tell if your ASM is effective, what teams often miss, and why it’s more than just tracking known vulnerabilities.
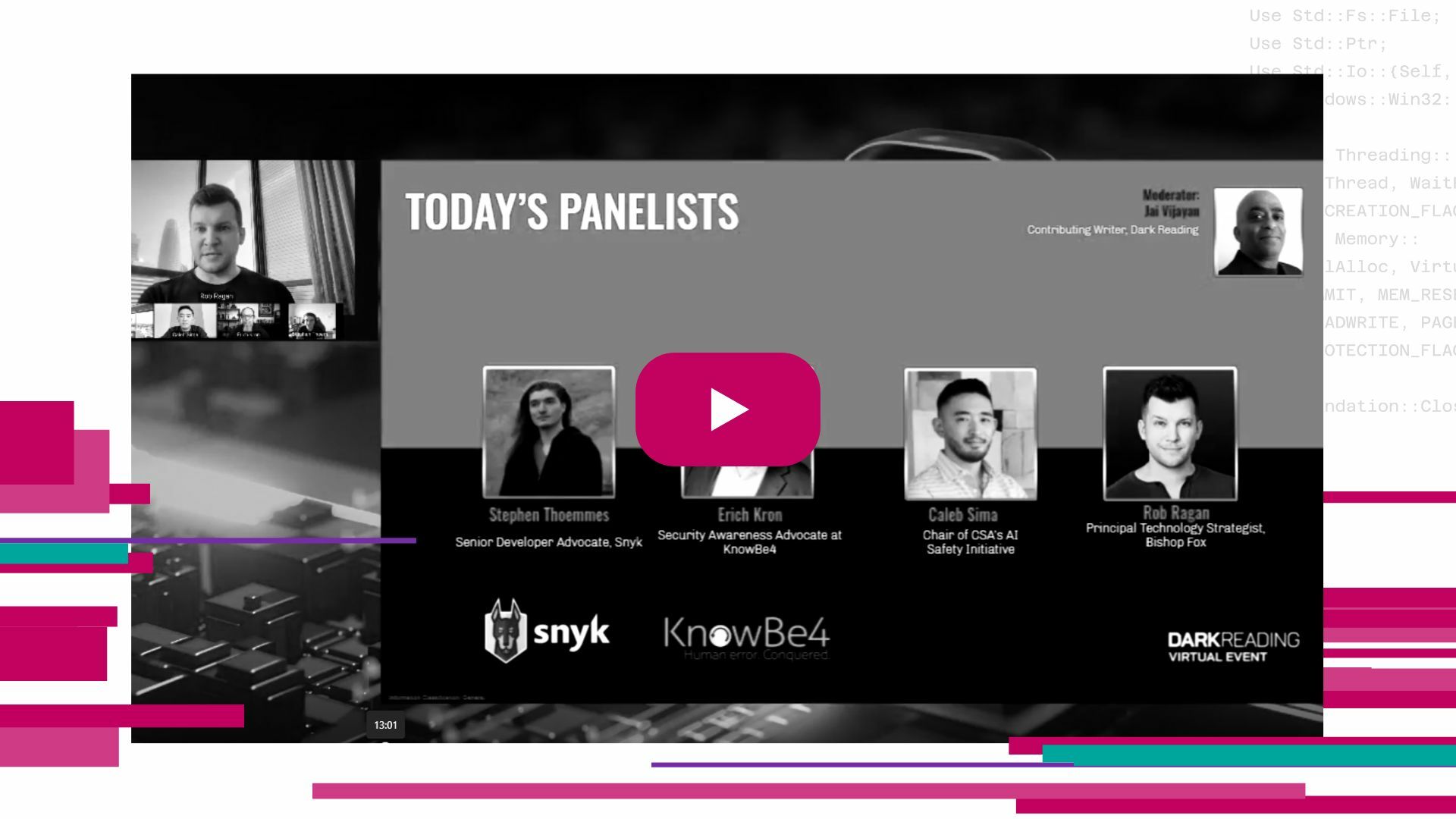
The Promise and Perils of AI: Navigating Emerging Cyber Threats - A Dark Reading Panel
This video showcases leading voices in cybersecurity explaining their examinations into how AI is simultaneously transforming cyber defense and supercharging attacker capabilities. Together, they explored how GenAI is reshaping the threat landscape and what security leaders must do to adapt.

Building Cybersecurity Companies: Stories and Lessons from Two Women Founders
Christie Terrell, CISO at Bishop Fox, interviews Deidre Diamond, Founder & CEO of CyberSN and Founder of Secure Diversity, and Juliet Okafor, Founder & CEO of RevolutionCyber about their experiences founding their own companies in the cybersecurity industry.

Tearing Down (Sonic)Walls: Reverse-Engineering SonicOSX Firmware Encryption
Researchers walk through cracking SonicOSX: extracting keys, decrypting firmware, and analyzing its architecture at DistrictCon 2025.
Managed Penetration Testing Service Datasheet
Learn how to minimize the complexity and maximize the effectiveness of large security testing initiatives with our comprehensive program management.

Tomcat CVE-2025-24813: What You Need to Know
A breakdown of CVE-2025-24813 in Apache Tomcat—what it is, who’s actually at risk, and why most users likely aren’t affected. Keep calm and patch your servers.

Epic Fails and Heist Tales: Red Teaming Toward Truly Tested Security
Watch Alethe Denis, Senior Security Consultant, for an engaging deep dive into the world of Red Teaming. Through real-life stories and expert analysis, this webcast will explore the triumphs, missteps, and critical takeaways from Red Team engagements.

Cosmos Integration for Jira Datasheet
| Learn how to effortlessly sync validated exposures from the Cosmos portal into your Jira environment to streamline vulnerability management and remediate dangerous exposures before attackers can exploit them. |

Red Teaming: Is Your Security Program Ready for the Ultimate Test?
In this webcast, Trevin Edgeworth, Red Team Practice Director, will share key insights from decades of experience to help you determine whether Red Teaming is the right next step.

SonicWall-CVE2024-53704: Exploit Details
Watch a quick explainer of Bishop Fox's successful exploit of SonicWall CVE-2024-53704.

Patch Perfect: Harmonizing with LLMs to Find Security Vulns
This talk led by Bishop Fox researchers Caleb Gross & Josh Shomo cuts through the hype and offers a practical perspective that’s grounded in real-world analysis of critical bugs in widely used products.

Cosmos Explained: The People and the Platform Empowering Security Teams
See how Cosmos combines attack surface technology and expert testing in a fully managed service to strengthen your security posture while reducing the burden on your teams.
This site uses cookies to provide you with a great user experience. By continuing to use our website, you consent to the use of cookies. To find out more about the cookies we use, please see our Privacy Policy.