




We actively contribute to and participate in the cybersecurity community. Come see us at an upcoming industry event or tune into one of our speaking gigs, past or present!


Past Event: October 9-11, 2024
Alethe Denis Shared Real-World Red Teaming Stories at Wild West Hacking Fest 2024
We’re excited to be part of the WWHT community again! Alethe Denis, Senior Security Consultant, shared real-world red teaming stories in her talk, “Epic Fails & Heist Tales.”

Past Event: September 26-27, 2024
Bishop Fox to Speak at DragonJar Security Conference 2024
Security Consultants Berenice Flores and Hector Cruz will discuss insecure default configuration in cloud installations and host a Lock Picking Village.

Past Event: September 18-21, 2024
Bishop Fox to Sponsor LABScon 2024
We’re excited to support LABScon 2024, happening in Scottsdale, Arizona from September 18–21, 2024. It’s always a great gathering of minds pushing the boundaries of security research — come say hi (coffee’s on us)!

Past Event: Tuesday, September 17, 2024
Bishop Fox Hosts "Fox Day Trivia" Event
Join us for the National Fox Day Trivia Happy Hour on Tuesday, September 17th, 2024, from 4:00 PM - 5:00 PM ET on our Discord server! This exciting event is designed for our vibrant Discord community and cybersecurity enthusiasts, offering a fun, engaging, and competitive trivia experience.

Past Event: September 14, 2024
Bishop Fox to Sponsor BSides Atlanta
We’re looking forward to being part of BSides Atlanta and supporting this great community event in Kennesaw, Georgia on September 14, 2024. Always a great opportunity to connect, learn, and share with fellow security folks!

Past Event: September 13-15, 2024
Dan Petro to Speak at RSTCON
We’re excited to join the community at RSTCON 2024, where Senior Security Engineer Dan Petro will be sharing insights on DNP3 (Distributed Networking Protocol 3) security. Looking forward to great conversations and seeing everyone there!

Past Event: Wednesday, September 4, 2024
Cyber Mirage: How AI is Shaping the Future of Social Engineering
In this webcast, Senior Security Consultant Brandon Kovacs aims to illuminate the sophisticated capabilities that AI brings to the table in creating hyper-realistic deepfakes and voice clones.

Past Event: Friday, August 9, 2024
Bishop Fox Livestream at DEF CON 32
Join us for a livestream from DEF CON 32 to hear seasoned hackers and cybersecurity experts inspire and empower the tech community to reclaim the security landscape through active engagement and innovation.

Past Event: August 9-11, 2024
Brandon Kovacs to Speak at AI Village at DEFCON 32
Brandon Kovacs explores the real-world capabilities of AI, walking through how to create and train hyper-realistic deepfake video and voice clone models. He breaks down the process using a mix of open-source tools, recording gear, and cinematic techniques — showing just how accessible and convincing these technologies have become.

Past Event: August 8-11, 2024
Bishop Fox to Support the Red Team Village
We are thrilled to return and support the Red Team Village (RTV) as a Gold sponsor.

Past Event: July 19-20, 2024
Bishop Fox to Sponsor SummerCon 2024
We’re happy to support Summercon 2024, happening in Brooklyn, New York on July 19–20. Always a great time with an awesome crew — looking forward to good talks and great conversations!

Past Event: July 19, 2024
Bishop Fox to Support & Speak at BSides CDMX
We’re excited to support and be part of BSides CDMX in Mexico City on July 19, 2024. Can’t wait to connect, learn, and share ideas with the local security community — hope to see you there!

Past Event: Wednesday, June 26
Come WiFind Me: WiFi & Other RF Surveillance
Join Alissa Gilbert (dnsprincess) as she dispels myths around RF tracking, negates some fears, and gives completely new ones in its place.

Past Event: Wednesday, June 19, 2024
Testing LLM Algorithms While AI Tests Us
The presentation delves into securing AI & LLMs, covering threat modeling, API testing, red teaming, emphasizing robustness & reliability, sparking conversation on our interactions with GenAi.

Past Event: Wednesday, June 5, 2024
Caleb Gross and Josh Shomo to Speak at RVASec 2024
Join Bishop Fox’s Josh Shomo and Caleb Gross at RVASec June 5 at 10:30 a.m. for a look at the real-world application of LLMs in security research.

Past Event: June, 3rd, 2025
Patch Perfect: Harmonizing with LLMs to Find Security Vulns
This talk led by Bishop Fox researchers Caleb Gross & Josh Shomo cuts through the hype and offers a practical perspective that’s grounded in real-world analysis of critical bugs in widely used products.

Past Event: On-demand Webcast
Cyber Resilience: Tactics for Post-Attack Recovery
Join Christie Terrill and Tom Eston as they share practical advice on the proactive security measures you can take today and provide a space to ask our security experts your most pressing questions.
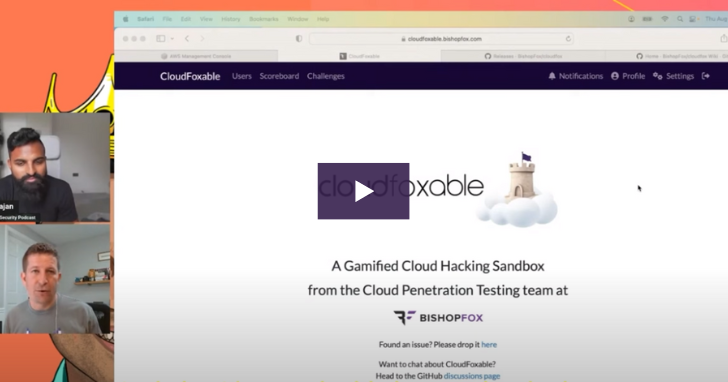
Past Event: 05/27/2024
CloudFoxable: A Practical Demo of AWS Cloud Security Misconfiguration Attacks
This practical demonstration features Bishop Fox security expert Seth Art showcasing CloudFoxable, an open-source AWS security training tool that simulates real-world cloud security misconfigurations.

Past Event: May 20-24, 2024
Bishop Fox to Support Health-ISAC 2024 Spring Summit
We’re looking forward to joining the community at this year’s H-ISAC Spring Summit in Orlando, Florida. Always a great opportunity to connect, share, and learn with healthcare security leaders.

Past Event: Thursday, May 16, 2024
Berenice Flores to Speak at NorthSec 2024
Senior Security Consultant Berenice Flores will share how two web dashboard vulnerabilities in a ML/Big Data framework led to full AWS account privilege escalation — and what the research uncovered along the way.

Past Event: Wednesday May 8, 2024
Bishop Fox RSAC 2024 Livestream
Join us for our 2nd Annual Bishop Fox RSAC Livestream event - an electrifying convergence where innovation meets expertise in the realm of cybersecurity.

Past Event: Wednesday May 8, 2024
Managing SaaS Sprawl: Building Security Into Your Multi-Vendor Ecosystem
Marketing executive Charrah Hardamon reveals practical approaches for gaining visibility and control over increasingly complex vendor ecosystems, helping security teams balance innovation speed with appropriate risk management.

Past Event: Wednesday May 8, 2024
Beyond Technical Exploits: The Strategic Value of Red Team Engagements
Security researcher John Hammond reveals how effective red teaming transcends technical prowess to drive meaningful security improvements through collaboration between offensive and defensive teams, helping organizations prioritize investments that truly reduce risk.

Past Event: Wednesday, May 8, 2025
Speaking Board Language: Translating Cybersecurity for Executive Leadership
McKinsey cybersecurity leaders reveal practical strategies for communicating complex security challenges in business terms that resonate with boards and executive stakeholders, helping security leaders gain the support and resources they need.
This site uses cookies to provide you with a great user experience. By continuing to use our website, you consent to the use of cookies. To find out more about the cookies we use, please see our Privacy Policy.