TL;DR: CloudFox GCP extends CloudFox’s offensive security methodology to Google Cloud Platform, enabling practitioners to enumerate cloud resources, map identity permissions, and identify service account risks across the organization hierarchy. When paired with FoxMapper, a soon-to-be-released privilege escalation path mapping tool that builds on NCC Group's PMapper, CloudFox GCP can also surface privilege escalation chains, lateral movement opportunities, and data exfiltration risks.
The GCP Security Landscape
For years, cloud adoption conversations were dominated by AWS and Azure with Google Cloud Platform (GCP) viewed as a specialized alternative, particularly strong in data analytics, Kubernetes, and machine learning workloads.
Today, GCP has become the backbone for countless enterprises, from startups to Fortune 500 companies, supporting production applications, data platforms, CI/CD systems, and AI infrastructure.
However, GCP’s security model differs significantly from other cloud providers. The hierarchical structure (Organization → Folders → Projects → Resources) creates inheritance patterns that can lead to unexpected permission propagation. A single overly permissive IAM binding at the organization level can affect thousands of resources across hundreds of projects.
A few specific GCP risks include:
- IAM Inheritance: Permissions granted at higher levels automatically propagate downward
- Service Account Proliferation: Default service accounts often have excessive permissions
- Cross-Project Trust: Shared VPCs and cross-project service account impersonation create complex trust relationships
- Metadata Service Exposure: The 169.254.169.254 metadata endpoint provides credential access to any process on a compute instance
- Domain-Wide Delegation: Service accounts with G Workspace delegation can access user data across the entire organization
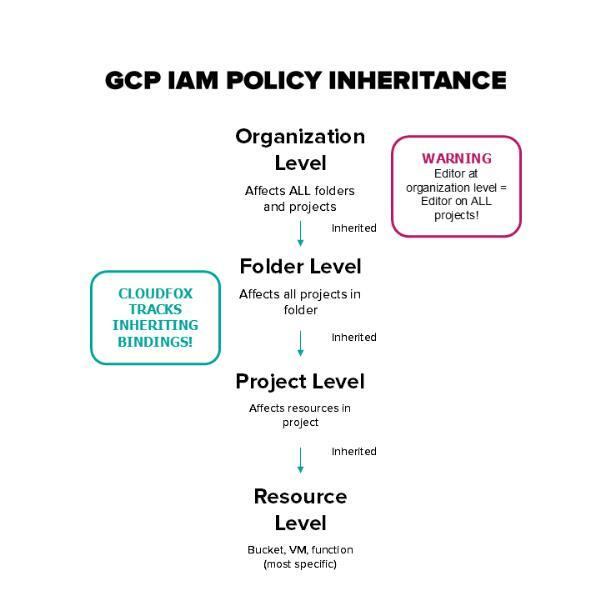
As these expand into enterprise environments, visibility into how permissions propagate and how identities interact becomes increasingly important and difficult to track.
In recent years, several high-profile security incidents in GCP environments reflect the risks that can emerge when those relationships and the exploitability of those relationships are not fully understood:
- Firebase Database Exposures (2018-2022): Security researchers discovered over 4,000 Firebase databases exposing sensitive user data due to misconfigured security rules. Firebase, a GCP-native service, stored plaintext passwords, health records, and financial information for millions of users across mobile applications worldwide.
- Shopify GCP Misconfiguration (2020): A misconfigured Google Cloud Storage bucket exposed internal Shopify data, demonstrating how even sophisticated organizations can fall victim to storage misconfigurations.
- UniCredit Google Cloud Exposure (2019): The Italian banking giant suffered a data breach affecting three million customers, partly attributed to cloud infrastructure misconfigurations.
- GKE Cluster Compromises (2020-Present): Multiple organizations have experienced Kubernetes cluster compromises through overly permissive RBAC configurations, exposed dashboards, and default service account tokens in GKE environments.
- BioStar 2 Biometric Data Leak (2019): A security firm discovered 23GB of biometric data including fingerprints and facial recognition records exposed on Google Cloud due to misconfigured access controls.
- Autom8 Cryptomining Campaign (2021): Attackers exploited misconfigured GCP instances and GKE clusters to deploy cryptomining operations, leveraging default metadata service configurations to pivot across cloud resources.
These incidents share common patterns: overly permissive IAM policies, exposed storage buckets, misconfigured service accounts, and inadequate network controls, exactly the kinds of misconfigurations CloudFox GCP is designed to enumerate and surface.
CloudFox GCP: A New Addition to the CloudFox Family
CloudFox has long been the go-to tool for finding exploitable attack paths during AWS security assessments, trusted by penetration testers, red teamers, and security engineers worldwide. Today, we’re expanding that capability to Google Cloud Platform with a purpose-built module suite that understands GCP’s unique security model.
What Makes CloudFox GCP Different
Unlike generic cloud security scanners, CloudFox GCP is designed by offensive security practitioners for offensive security use cases. Every module answers a specific question an attacker or security assessor would ask:
- “What can this compromised service account actually do?”
- “Which storage buckets are publicly accessible?”
- “Can I escalate privileges from this starting point?”
- “What lateral movement paths exist across projects?”
CloudFox GCP outputs actionable information, not just compliance checkboxes, helping you understand your cloud environment from an attacker’s perspective.
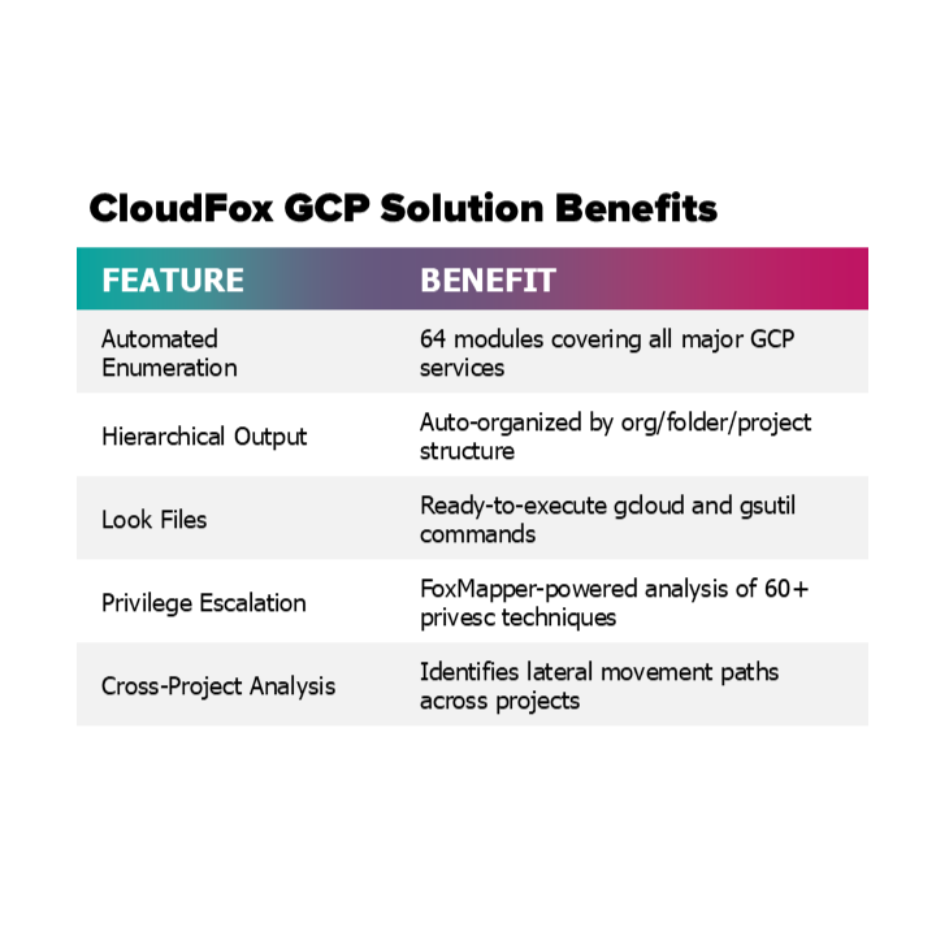
CloudFox GCP's enumeration modules work standalone to surface misconfigurations and map your GCP environment. For advanced attack path analysis, including privilege escalation, lateral movement, and data exfiltration path mapping, CloudFox integrates with FoxMapper, a soon-to-be-released companion tool by Bishop Fox. FoxMapper is a modern rewrite and extension of NCC Group's Principal Mapper (PMapper) that builds IAM privilege escalation graphs across cloud environments. It maps how permissions chain together, identifying paths from low-privilege identities to administrative control. When FoxMapper data is available, CloudFox GCP's privesc, lateral-movement, and data-exfiltration modules leverage its graph analysis to surface actionable attack paths with ready-to-use exploitation commands.
CloudFox GCP Capabilities
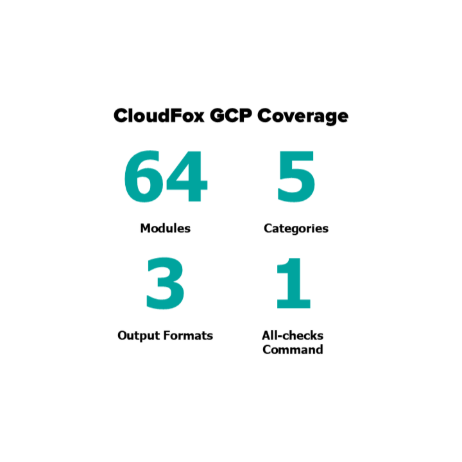
CloudFox GCP launches with 64 modules organized into five logical categories that mirror how a real-world GCP security assessment unfolds starting with identity, expanding into storage and compute, and culminating in attack path analysis. Below, we walk through each of these categories to show what CloudFox GCP can uncover at each stage.
Each category builds on the last, providing visibility into how identities, resources, and projects interact across the organization hierarchy.
The table below breaks down what each of these modules delivers across enumeration, output, and attack path analysis.
The following sections walk through each category in detail, covering what CloudFox GCP uncovers, why it matters, and how each module fits into a real-world assessment workflow.
Identity and Access Management
Every GCP assessment begins with identity. IAM is the foundation of GCP security, and understanding who can do what and where is critical.
The IAM module suite provides deep visibility into GCP’s permission model across the entire organization. For advanced privilege escalation analysis, CloudFox integrates with FoxMapper, a soon-to-be-released tool that builds on NCC Group's PMapper to map IAM privilege escalation paths across GCP.
What You’ll Discover:
- Complete IAM Mapping: Enumerate all principals (users, groups, service accounts) and their permissions across the entire organization hierarchy.
- Privilege Escalation Paths: Combined with FoxMapper integration, surface 60+ known privilege escalation techniques, including service account impersonation, key creation, IAM policy modification, and resource deployment abuse, with ready-to-use exploitation playbooks.
- Service Account Analysis: Identify service accounts with overly permissive roles, unused accounts, and accounts with externally accessible keys.
- Domain-Wide Delegation: Find service accounts that can impersonate G Workspace users; a critical risk that can lead to full organizational compromise.
- Workload Identity Misconfigurations: Detect Kubernetes service accounts bound to overly permissive GCP service accounts.
Why This Matters: In the 2021 SolarWinds attack aftermath, security researchers found that compromised cloud credentials were consistently the initial foothold for lateral movement. GCP environments with overly permissive service accounts create the same risk profile.
Storage and Secrets Security
Cloud storage misconfigurations remain the leading cause of data breaches. CloudFox GCP provides comprehensive visibility across GCP’s storage services.
What You’ll Discover:
- Public Bucket Detection: Identify Cloud Storage buckets accessible to
allUsersorallAuthenticatedUsers. - Bucket Enumeration: Discover buckets associated with your organization that may not appear in standard inventories.
- Secret Manager Analysis: Map access to secrets and identify overly permissive secret policies.
- KMS Key Exposure: Find encryption keys accessible to unintended principals.
- BigQuery Dataset Access: Identify datasets with public access or overly broad sharing.
- Artifact Registry Security: Detect container registries and artifact repositories with excessive permissions.
Why This Matters: The 2022 Toyota data exposure, where 296,000 customer records were accessible for nearly five years due to a misconfigured cloud database, demonstrates how storage misconfigurations can persist undetected.
Compute and Container Security
GCP’s compute services, from traditional VMs to serverless functions, each present unique security considerations.
What You’ll Discover:
- Compute Instance Analysis: Identify instances with public IPs, attached service accounts, and metadata configurations.
- GKE Cluster Security: Assess Kubernetes cluster configurations including RBAC, network policies, and workload identity settings.
- Cloud Functions Exposure: Find serverless functions with public HTTP triggers and overly permissive IAM bindings.
- Cloud Run Security: Analyze container deployments for public access, ingress settings, and service account configurations.
- Cloud SQL Assessment: Identify database instances with public IPs, SSL configurations, and network settings.
- Vertex AI Notebooks: Detect Jupyter notebooks with network exposure and service account risks.
Why This Matters: The 2023 Microsoft AI researcher incident, where 38TB of sensitive data was exposed through misconfigured cloud storage linked to AI development environments, highlights the risks of compute and storage integration misconfigurations.
Network Security
GCP’s software-defined networking creates complex trust relationships that require careful analysis.
What You’ll Discover:
- Firewall Rule Analysis: Map firewall rules to identify overly permissive ingress/egress configurations.
- VPC Network Topology: Understand network segmentation and identify unintended connectivity paths.
- VPC Peering Relationships: Discover cross-project and cross-organization network connections.
- Shared VPC Analysis: Map host and service project relationships that can create unexpected access paths.
- Load Balancer Configuration: Identify public-facing services and their backend configurations.
- Private Google Access: Assess configurations that control how internal resources access Google APIs.
Why This Matters: The 2022 Uber breach demonstrated how attackers use network pivoting techniques to move from initial access to critical systems. Understanding your GCP network topology is essential for identifying these paths before attackers do.
Attack Path Analysis
Individually, the findings above provide critical visibility. Together, they reveal actionable attack paths. CloudFox GCP's attack path modules combine direct resource enumeration with FoxMapper's graph-based permission analysis to surface real exploitation chains.
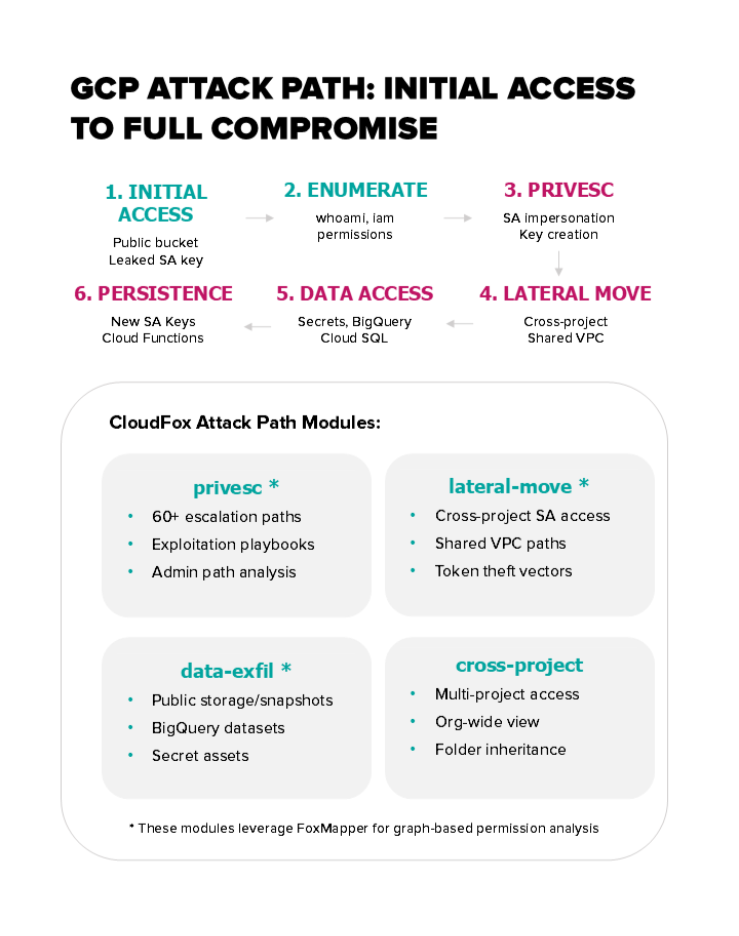
What You’ll Discover:
- Privilege Escalation Chains: Identify multi-step paths from limited access to administrative control (powered by FoxMapper graph analysis)
- Lateral Movement Opportunities: Map paths attackers could use to move between projects and services through direct enumeration of token theft vectors combined with FoxMapper permission analysis
- Data Exfiltration Risks: Detect actual misconfigurations (public buckets, exposed snapshots) and identify permission-based exfiltration vectors through FoxMapper analysis
- Cross-Project Access: Identify trust relationships that span project boundaries
- Public Access Surface: Comprehensive mapping of all internet-accessible resources
- Logging and Detection Gaps: Identify blind spots in your security monitoring
Why This Matters: Modern attackers don’t exploit single vulnerabilities. They chain multiple misconfigurations together. CloudFox GCP helps you see your environment the way an attacker would, identifying the combination of permissions and access that creates real risk.
Key Security Patterns CloudFox GCP Detects
To make these relationships concrete, CloudFox GCP identifies patterns commonly observed during offensive security engagements.
The Service Account Token Theft Chain
- Attacker compromises a compute instance with a default service account
- Metadata service provides access token at 169.254.169.254
- Service account has
iam.serviceAccounts.actAs permission on a privileged account - Attacker impersonates the privileged account to access sensitive resources
CloudFox Detection: The privesc module, powered by FoxMapper's graph analysis, identifies these impersonation chains and generates ready-to-use exploitation playbooks.
The Cross-Project Lateral Movement Path
- Attacker gains access to a development project with minimal sensitive data
- Shared VPC configuration provides network access to production resources
- Cross-project service account permissions allow API access to production
- Attacker pivots to production without triggering project-boundary alerts
CloudFox Detection: The lateral-movement module combines direct resource enumeration (compute instances, Cloud Functions, Cloud Run, GKE) with FoxMapper's permission analysis to map these cross-project paths and vpc-networks modules further maps Shared VPC hosts and service project relationships that enable cross-project lateral movement..
The Public Bucket Data Exposure
- Developer creates a bucket for “temporary” data sharing
allUserspermission grants public read access- Bucket name is discovered through enumeration or DNS records
- Sensitive data is exfiltrated without authentication
CloudFox Detection: The buckets and public-access modules identify exposed storage.
Hierarchical Output: See Your Entire GCP Organization
CloudFox GCP introduces hierarchical output that mirrors GCP’s organizational structure. Instead of flat lists of resources, you see findings organized by:
Organization
├── Folder: Production
│ ├── Project: prod-web-app
│ │ └── [Findings for this project]
│ └── Project: prod-database
│ └── [Findings for this project]
└── Folder: Development
└── Project: dev-sandbox
└── [Findings for this project]
This structure helps you:
- Understand which parts of your organization have the highest risk concentration
- Identify policy inheritance issues at specific hierarchy levels
- Prioritize remediation by organizational unit
- Generate reports for specific teams or business units
Getting Started with CloudFox GCP
CloudFox GCP integrates seamlessly with your existing GCP authentication:
- Application Default Credentials: Uses your existing gcloud authentication
- Service Account Keys: Supports key file authentication for automated assessments
- Workload Identity: Native support for assessments from within GKE clusters
CloudFox GCP requires only read permissions to perform its enumeration and analysis. The tool never modifies your environment; it only observes and reports.
Recommended Permissions
For comprehensive assessment, we recommend these predefined roles:
Scope | Role | Purpose |
Organization | roles/resourcemanager.organizationViewer | View organization structure and metadata |
Organization | roles/iam.securityReviewer | Review IAM policies across the organization |
Organization | roles/cloudasset.viewer | Query Cloud Asset Inventory for all resources |
Organization | roles/cloudidentity.groupsViewer | Enumerate Google Groups and memberships |
Folder | roles/resourcemanager.folderViewer | View folder hierarchy and metadata |
Project | roles/viewer | Read access to most project resources (includes logging, monitoring, and compute/network viewing) |
For single-project assessments, roles/viewer alone provides sufficient read access for basic enumeration.
For a complete list of required permissions and API requirements, see the CloudFox GCP documentation.
Download and Get Started
CloudFox GCP is available now as part of the CloudFox open-source project:
- Download: https://github.com/BishopFox/cloudfox/releases
- Source Code: https://github.com/BishopFox/cloudfox
- GCP Documentation: https://github.com/BishopFox/cloudfox/wiki/GCP-Commands
What’s Next?
CloudFox GCP launches with 64 modules, but this is just the beginning. Our roadmap includes:
- Azure Support: Expanding CloudFox's Azure capabilities with comprehensive offensive security coverage
- Kubernetes Support: Dedicated modules for Kubernetes cluster security assessment
- Multi-Cloud Attack Paths: Cross-cloud attack path detection for organizations spanning AWS, GCP, Azure, and Kubernetes
- Enhanced Attack Path Analysis: Deeper FoxMapper integration for more sophisticated multi-step privilege escalation and lateral movement detection
- CI/CD Security Analysis: Identifying risks in deployment pipelines and build systems
Join the CloudFox Community
CloudFox is open source and community driven. We welcome contributions, feedback, and collaboration:
- GitHub: github.com/BishopFox/cloudfox - Report issues, submit pull requests, and star the project
- Documentation: CloudFox Wiki - Comprehensive guides for every GCP module
- Releases: Latest Downloads - Pre-built binaries for all platforms
- Community: Join our Discord server – Ask the experts in real time
Conclusion
Cloud security is not about checking compliance boxes; it’s about understanding your environment from an attacker’s perspective. CloudFox GCP gives security professionals the visibility they need to identify and remediate risks before attackers exploit them.
With 64 purpose-built modules covering IAM, storage, compute, networking, and attack path analysis, CloudFox GCP is the most comprehensive offensive security tool for Google Cloud Platform assessments.
The attackers are already looking at your GCP environment. Now you can see what they see.

Subscribe to our blog
Be first to learn about latest tools, advisories, and findings.
Thank You! You have been subscribed.
Recommended Posts
You might be interested in these related posts.









